Nostr has been taking the Bitcoin world by storm over the past few months, and with it comes a chance to correct the mistakes of the current social media paradigm. While the actual use-cases for Nostr are practically limitless, the overwhelming majority of usage today has come in the form of a censorship-resistant and Lightning-centric social media platform built around user choice. Nostr takes a novel approach to its network design, and we want to be sure that Nostr users like yourself are well-equipped to use Nostr in a way that preserves your privacy and security from the start.
What is Nostr?
Nostr is a new protocol (think TCP/IP or HTTP, like what your browser uses) that focuses on the very simple goal of publishing and reading events in a distributed way. It does this by allowing anyone to run a client (how you read or write events) and/or a relay (how you share events with others). Each relay communicates only with users who choose to send or receive events using it and not with other relays, a significant departure from Bitcoin’s model – called a “gossip” model, where all servers share events with all other servers they know – and the approach taken by the Fediverse, where servers that can communicate and share events but do not have to.
This new protocol is extremely simple and diverse by design, allowing a plethora of apps and services to be built on top of it, but the most traction so far has come from its use as a social media platform. Nostr provides a strong base for a user-centric social media platform, as you, the user, have complete control over where your posts are shared (which relays), which users you see or don’t see in your feed (by following specific users or only reading from specific relays), and what client you choose to use to post or consume content.
When you post to Nostr, your client simply translates the content you write into a format called JSON, signs it with your private key to prove it’s from you and cannot be tampered with, and publishes it to relays you’ve selected. Everyone who follows you and connects with relays you publish to will see your content in their timeline exactly as intended. When you browse Nostr, you see only content from people you choose to follow, in chronological order, without advertisements or algorithmic wizardry causing issues. Simple. Clear. Social media as it should be.
If you want to learn more about Nostr, you can read some excellent resources below:
- “Why Nostr Matters” – Jameson Lopp
- nostr.com
- nostr.how
- Awesome-nostr, a curated list of Nostr projects and resources
Nostr’s privacy tradeoffs
The proxied-relay approach that Nostr takes is excellent at decentralization and censorship-resistance, but one thing it doesn’t do well is protect a user’s privacy by default. Because you need to connect to many different relays to communicate with most people using Nostr today, you’ll be exposing your IP address (your unique identifier on the internet) to every relay you connect to, directly associating your IP address to your digital identity on Nostr. This could be used to connect your Nostr identity with other online activity, connect multiple Nostr identities you control together without your consent, and even give the relay operators a rough idea of where you live.
Another key issue with the approach taken by Nostr is that there is no central server used for hosting media like pictures and videos, so users have to upload media to a server of their choice to share it. As a result, your Nostr client will have to connect to any number of untrusted servers hosting media to properly show you pictures and videos in your feed. While this does remove trust in a centralized server, it also exposes you to tracking or malicious content from third parties that you may or may not want to connect to. Thankfully, most Nostr clients are starting to prevent loading of content from untrusted sources, but this still poses a broad risk to your privacy and security.
Lastly, there are two more minor privacy caveats with Nostr that are important to know, but don’t necessarily present a problem for the average user. The first is that direct messages in Nostr use public events where the message content is encrypted to the recipient’s private key, meaning that while all message content is private by design, the metadata about who you talk to, when, is completely public information. The second minor privacy issue in Nostr is that Zaps, a Lightning tip sent for a specific note on Nostr to show that you loved the post, are public by default and reveal the amount, timing, and any comment included to the entire Nostr network. While this is the default, clients like Damus and Amethyst are working on ways to allow you to send “private Zaps” which encrypt all information except time and amount to the recipient, hiding the sender and any comments from everyone else on Nostr.
Protecting your keys
One of the foundational ways to preserve your privacy involves making sure that no one else ever gets access to your private keys. In Nostr, in order to access your account, post notes, and respond to others, you have to be able to sign events on the Nostr network with the correlated private key for your account. That means that every Nostr app requires a way to sign using your private key, leading to less than ideal security with many of the current approaches.
When approaching Nostr, you should aim to minimize how often you expose your private key to apps and restrict access as much as possible to your private key. In order to limit how often you expose your private key to apps, the best way on mobile is to choose a client, sign in with your private key, and stick with it if at all possible. Unfortunately, you’ll currently have to copy and paste (or manually type out) your private key (the key starting with ‘nsec’) to sign into mobile apps, but won’t need access to your private key on mobile after the initial sign-in.
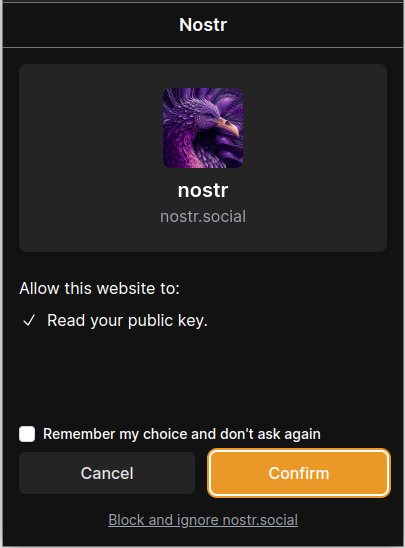
When you’re using desktop apps, particularly web apps like iris.to or nostr.social, you can limit exposure of your private keys by using a browser extension to store your private key in an encrypted manner and authorize access to it. That way, you can paste your private key into a trusted extension once and use any web app you like after that without directly exposing your private key to each app. We recommend the most popular and trusted extensions below:
- Nos2x (Chrome/Brave-only)
- Nos2x is an extremely simple extension for key management without any bells or whistles
- If you’re on Firefox, you can use this fork
- Alby
- The popular Alby extension added native Nostr key support, and pairs well with it’s Lightning functionality for Nostr Zaps
- Flamingo (Chrome/Brave-only)
- Flamingo is another simple Nostr extension with a beautiful UI
While we’re working on some unique ways to leverage Passport for Nostr key management, the best way to store your private key for Nostr will be to treat it like a sensitive password and store it in an end-to-end encrypted password manager like Bitwarden. Bitwarden is an amazing tool for managing your online life through storing usernames, passwords, and email addresses for all of your accounts and auto-filling them via their browser extension, and Nostr private keys are a great fit. Bitwarden is free and open-source, and uses strong end-to-end encryption to ensure that even if Bitwarden was malicious they couldn’t view what sites you access or any of your login information. You can easily store your Nostr private key as an item in Bitwarden, allowing you to enter it as needed on desktop or mobile easily.
Protecting your IP address
The next key step to take is to prevent relays and media hosting servers from learning your true IP address, and the easiest way to do that is to use a trustworthy and dependable VPN provider. While a VPN provider isn’t a perfect solution to network privacy issues, it does allow you to shift the trust from your network provider (home ISP, mobile carrier, etc.) to a 3rd-party you trust more than them (and that don’t have your personal information or address). Once you’re using a VPN, you’re actively preventing the sites, apps, and tools you interact with online from learning your home IP address and connecting all of your activities back to you.
Our team is a big fan and many of us are users of two well-known VPN providers in the space which we’ve linked below for easy reference. Both IVPN and Mullvad accept Bitcoin (on-chain and Lightning) for subscriptions and require no information from you to create an account, not even an email address!
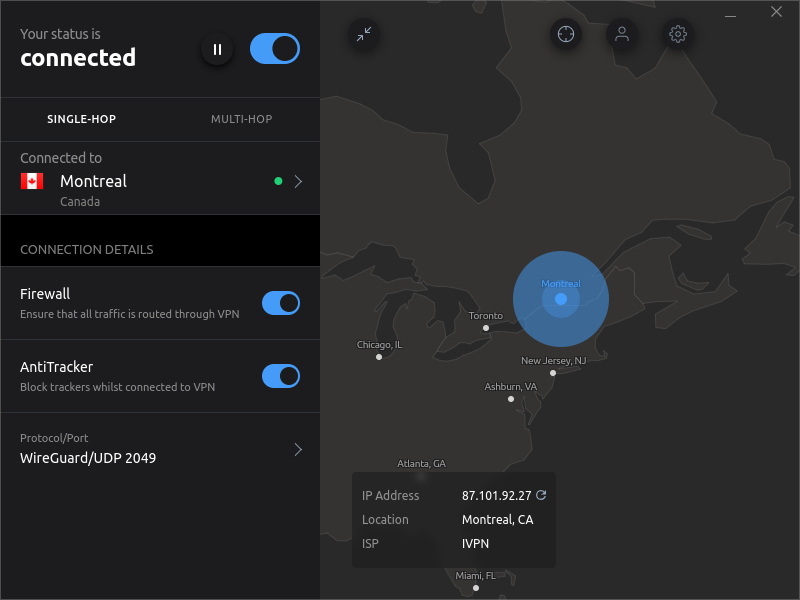
Please note that we have no direct affiliation with either provider and don’t profit off of your use of either, we just love their approaches and use them ourselves.
Choosing the right relays
Nostr takes the idea of self-sovereignty and personal responsibility as a core ethos, as you are in complete control of your data and your usage of the protocol. As each Nostr relay you connect with gets information about your IP address (hopefully just a VPN address if you followed the above recommendation), when you’re using Nostr, when you publish events, and who you interact with. While much of this information is public – and has to be so for a useful social media platform – being able to selectively reveal this information is an important benefit of Nostr.
While relay selection is certainly a personal preference as it changes what notes you can view and who can see your notes, limiting it to the bare minimum provides better privacy and generally better performance in your Nostr clients at the same time. The use of paid relays can also be helpful, as they limit spam and access to your public data behind a paywall. The list of relays and their usefulness changes frequently at this early stage in the network’s development, but we’ll provide a few recommendations below that are widely recommended:
- nostr.wine
- Nostr.wine is a paid relay that has a stellar reputation and a unique additional service that paid users can leverage
- Their filter/broadcast service allows you to publish events to the most popular relays through their relay
- More on their filter/broadcast service here
- nostr.mutinywallet.com
- This relay is actually just a proxy that publishes events for you to all known relays using a tool called Blastr
- This can be a great single write-only relay, ensuring your notes make it to pretty much the entire Nostrverse
- Note that if you do use only this relay proxy to write to, you do open up censorship as they could choose not to relay your events for some reason! If that’s a concern for you, consider writing to multiple relays.
- relay.nostr.band
- This relay applies a trust-based spam filter to all events, providing a much better global feed than most and serves as a good read-only relay
Adding these relays to your client will vary depending on which client you choose, so please check out the documentation of your favorite client or check in the settings! You usually will have to add a ‘wss://’ before the relay address as well.
Getting started with Nostr
If you’ve read through this post and want to jump into using Nostr, we’ve learned a few things as team members have jumped onto the Nostr train. We’ll drop recommendations based on this below in a rapid-fire style, but feel free to reach out with questions and we’d be happy to help point you in the right direction!
Choosing a client
Choosing a client is ultimately down to personal preference and depends on what platform you use (Android, iOS, Windows, etc.), but some of our favorites are:
- Amethyst (Android-only)
- Vitor Pamplona, the lead dev, has done a fantastic job building out Amethyst and it feels like he releases a new major improvement every day. Amethyst is a fantastic client top-to-bottom, and is what both Seth For Privacy and Bitcoin QnA use on our team.
- Damus (iOS-only)
- Damus has become a huge part of Nostr adoption, driving new features and bringing a snazzy Nostr experience to the Apple crowd.
- snort.social (web client)
- snort.social is a great client for using on desktop or on mobile as a progressive web app, and is quickly improving and innovating as well.
- Iris.to (web client)
- Iris.to is another great web client and is quickly becoming the go-to for web.
Verifying your Nostr account
Nostr takes a very different approach to Twitter, allowing all users to be “verified” through the use of DNS and a simple web server. While we definitely recommend pursuing the fully self-sovereign approach to verifying your account on Nostr and hosting it yourself, we recognize that not everyone can do that so we’ve included some trusted Nostr verification services as well below:
- For more info on verification, you can read more here
- NIP-05 Simple Guide (self-hosted)
- This guide walks you through the process of setting up verification start to finish, and is recommended widely.
- Easy-nip5 (self-hosted)
- Our very own Seth For Privacy has created an easy-to-use way to do your own self-hosted verification using Docker, allowing you to quickly set up the full verification on a VPS with your own domain name
- Bitcoiner.chat (trusted)
- Bitcoin QnA has set up an easy to use tool to get a verified account using his domain, bitcoiner.chat, for free! This is an excellent solution for those of you who can’t self-host your own verification, and is provided by one of the most trustworthy people in the space, if we do say so ourselves.
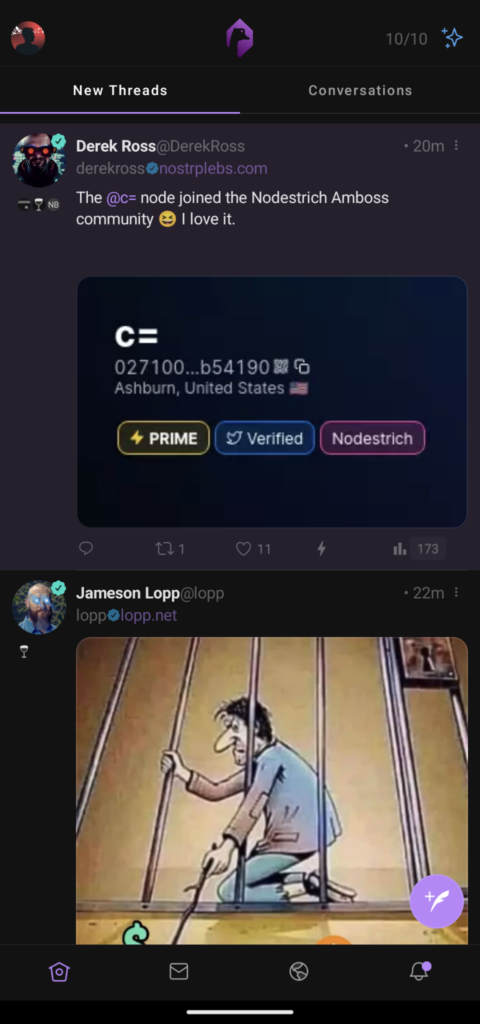
- Nostr Plebs! (trusted)
- Nostr Plebs is one of the original NIP-05 verifiers, and is run by a fantastic Nostrich named Derek Ross.

Conclusion
We’re thrilled to watch the progress being made in a Bitcoin-centric social media platform that puts the user first, as it embodies so much of what Foundation is all about. We hope that this short guide helps you get started with Nostr in a way that allows you to preserve your privacy and security from the start, and we look forward to seeing you all over there.
If you’d like to follow us on Nostr you can find our official company account along with a few of our team members below!
- Foundation
foundationdevices.comnpub1s0vtkgej33n7ec4d7ycxmwt78up8hpfa30d0yfksrshq7t82mchqynpq6j
- Seth for Privacy
[email protected]npub1tr4dstaptd2sp98h7hlysp8qle6mw7wmauhfkgz3rmxdd8ndprusnw2y5g
- BitcoinQnA
[email protected]npub15c88nc8d44gsp4658dnfu5fahswzzu8gaxm5lkuwjud068swdqfspxssvx
- nickmonad
nickmonad.blognpub1tln5mjd8xjd7rqnfqp7cu77lwkvcd89kwllr7fu5a0vzru2xl6qssuq0v6
- Jack Smith
npub1d8mwl982z209f3zf856t87z36gmavgctw59r30pxr880emxmjy6sq4qtwj